Data access governance is the master plan that ensures the right people have the right level of access to the right data, precisely when they need it. It’s not about locking everything down; it's about managing access intelligently and securely. This is absolutely essential as data piles up and security threats become more sophisticated.
What Data Access Governance Really Means

Think of it like managing the keys to a huge corporate building. You wouldn't give every employee a master key that opens every single door, would you? Of course not. Access is handed out based on a person's role and what they actually need to do their job.
For a practical example, consider a new marketing analyst. They need access to customer behavior data in your data warehouse to analyze campaign effectiveness. Data access governance is the system that grants them read-only access to specific marketing tables, but blocks them from seeing sensitive PII in the finance or HR databases.
Data access governance applies this exact same logic to your digital world. It's the system that defines who gets the "keys" (permissions) to specific "rooms" (databases, files, apps) and why they need them. Without a solid system, you’re basically handing out master keys to everyone, leaving your most sensitive information wide open to accidents, misuse, or worse, a targeted attack.
Why It Matters Now More Than Ever
Let's be blunt: having a formal approach to data access isn't a "nice-to-have" anymore. Trying to manage permissions manually is a recipe for disaster in today's data-heavy environments. Companies are getting hit with a perfect storm of challenges that make strong governance a matter of survival.
Here are the big drivers:
- Exploding Data Volume: Experts predict we'll hit 180 zettabytes of data by 2025. Manually keeping track of who can see what in that ocean of information is flat-out impossible. You need automation and clear rules to have any hope of keeping up.
- Complex Cloud Environments: Your data isn't neatly tucked away in one server room anymore. It's scattered across multiple clouds like AWS and Azure, various SaaS apps, and on-premise systems. This creates a fragmented mess that's incredibly difficult to control.
- Rising Security Threats: Data breaches are happening more often and costing more than ever before. A robust data access governance program is one of your best lines of defense against both skilled hackers and internal threats.
- Strict Regulatory Demands: Laws like GDPR and CCPA come with massive fines for getting it wrong. Being able to prove you have tight control over who can touch personal data isn't just a good idea—it's a core legal requirement.
A successful data access governance strategy goes far beyond just saying "yes" or "no" to access requests. It’s about creating end-to-end visibility, traceability, and control over how your data is actually used by anyone, anywhere in the organization.
The Three Pillars of Data Access Governance
A strong data access governance strategy is built on three core pillars. Each one is connected, and together they create a powerful framework for managing and securing your data. Think of them as the three legs of a stool—if one is weak, the whole thing topples over.
Understanding these pillars helps clarify what a complete governance program needs to accomplish.
| Pillar | Description | Key Function |
|---|---|---|
| Visibility & Monitoring | The ability to see who has access to what, how they got it, and what they’re doing with it in real-time. | Provides the foundational awareness needed to spot risks, identify strange behavior, and make smart decisions about access rules. |
| Policy & Control | The process of defining and enforcing access rules based on business roles, context, and risk levels. | Translates your business and security needs into consistent, automated controls that work across all your different systems. |
| Automation & Remediation | Using technology to handle access requests, reviews, and—critically—the automatic removal of permissions that are no longer needed. | Cuts down on manual work, gets people the access they need faster, and instantly closes security holes like old, forgotten accounts. |
By building out these three pillars, an organization creates a system that doesn't just protect its valuable data. It also empowers employees to get the access they need to do their jobs, all while keeping everything efficient and secure.
Embedding Core Principles into Your Strategy

True data access governance isn't a one-off project or a simple checklist. It's a deep-seated cultural shift, guided by core principles that shape every single decision about your data. These ideas are the bedrock of any secure and efficient framework, moving you from constantly putting out fires to proactively controlling your data environment.
One of the most foundational concepts is the Principle of Least Privilege (PoLP). At its heart, PoLP is simple: a user should only have the absolute minimum level of access—or permissions—they need to do their job. It's not about being suspicious of your team; it's just smart, defensive security design.
By tightly restricting access from the get-go, you dramatically shrink your potential attack surface. For example, if a marketing specialist's account is compromised, the intruder can only access campaign performance dashboards, not the entire customer database with credit card info. This kind of containment is absolutely critical for blunting the impact of a breach.
Actionable Insight: Applying The Principle Of Least Privilege
Putting PoLP into practice requires a real, granular understanding of what people actually do. You can't grant "minimal" access if you don't know what minimal looks like for each role.
- Actionable Step 1: Start at Zero. When a new employee joins, their account should have zero access to any sensitive data by default. You then deliberately add specific permissions based on a documented request tied to their job responsibilities.
- Actionable Step 2: Use Role-Based Access Control (RBAC). Instead of assigning permissions one-by-one, create roles like "Finance Analyst" or "Marketing Manager." Assign permissions to the role. This simplifies management and ensures consistency. For instance, any user assigned the "Finance Analyst" role automatically gets read-only access to the financial reporting database.
- Actionable Step 3: Implement Time-Bound Access. For a contractor working on a three-month project, grant access that automatically expires on their last day. This simple step prevents the slow, dangerous creep of unnecessary permissions.
This disciplined approach reframes access from something that's assumed into a deliberate, justified privilege, which directly strengthens your entire governance posture.
Another key idea is the Separation of Duties (SoD). This principle is all about preventing any single person from having end-to-end control over a critical process. Its goal is to slash the risk of internal fraud or a single catastrophic error.
By spreading tasks and their associated permissions across multiple people, you build a natural system of checks and balances. No one person holds all the keys, making it much harder to execute—and hide—malicious activity.
A Practical Example Of Separation Of Duties
Imagine a standard payment process in a company. A solid SoD framework would make sure that:
- Employee A can create a payment request for a vendor invoice.
- Employee B must approve that request after verifying the invoice is legitimate.
- Employee C is the only one authorized to actually execute the payment transfer.
In this setup, no single employee can invent a fake invoice, approve it, and pay themselves. It’s a simple but incredibly powerful concept that’s non-negotiable in financial controls, and the exact same logic applies to data. A database admin might be able to create new user accounts, but they shouldn't be able to grant sensitive data permissions without a separate approval from a designated Data Owner.
Finally, any strong strategy is built on continuous access reviews and robust data classification. People's roles change. They join new projects, finish old ones, or leave the company. Regular, scheduled reviews are essential to ensure that existing permissions are still relevant and necessary.
This is where data classification becomes so important. You can't protect what you don't understand. By classifying data into tiers—like "Public," "Internal," and "Confidential"—you can focus your most stringent controls where they matter most. This dovetails perfectly with the ideas in our guide on data architecture principles, which highlights how a well-structured system is far easier to govern. A clear classification scheme makes your access reviews faster and more effective, keeping your governance strategy sharp and relevant.
Building Your Data Access Governance Framework
Alright, let's move from theory to action. It's one thing to talk about the principles of data access governance, but it's another thing entirely to build a working framework. This isn't about creating some rigid, bureaucratic checklist that everyone ignores. Instead, think of it as engineering a living, breathing process that protects your most valuable assets while still letting your business move fast.
The very first step? Figure out who is responsible for what. Data governance is a team sport, not a solo mission for the IT department. You need people who actually understand the business context of the data they use every day. If you skip this, your policies will be completely disconnected from reality, and they'll gather dust.
Actionable Insight: Define and Assign Key Roles
For this to work, you need champions who are accountable for specific data domains. Two roles are absolutely essential here: the Data Owner and the Data Steward. They might sound similar, but their jobs are distinct and designed to complement each other.
-
Data Owners: These are your senior leaders or managers. They are ultimately accountable for the data within their business unit. Practical Example: The Chief Financial Officer (CFO) is the natural owner of all financial data. They don't manage permissions day-to-day, but they set the rules, sign off on high-level access policies, and are responsible for its quality and security.
-
Data Stewards: These are your hands-on subject-matter experts. A Data Steward is someone who truly understands the data's meaning, its quirks, and how it’s used. Practical Example: A senior financial analyst who works with revenue data daily would be the Data Steward. They are tasked with implementing the owner's policies, defining data quality rules, and reviewing access requests for the finance datasets.
Think of it like this: the Data Owner is concerned with the "what" and "why," while the Data Steward handles the "how."
A well-structured framework clearly delegates authority. By assigning owners and stewards, you ensure decisions about data access are made by those with the most relevant business knowledge, not just by an IT admin who lacks context.
Actionable Insight: Adopt a Risk-Based Approach
If you try to lock down every single piece of data with maximum security from day one, you'll fail. It’s overwhelming, inefficient, and a surefire way to alienate everyone. A much smarter way to start is by adopting a risk-based approach. Focus your initial efforts where it matters most—on the data that would cause the most damage if it leaked.
This means you need to identify and classify your "crown jewels" first. Actionable Step: Create a data inventory and start tagging your most sensitive assets:
- Personally Identifiable Information (PII): Customer names, addresses, social security numbers.
- Financial Data: Revenue reports, payroll information, corporate financial statements.
- Intellectual Property (IP): Proprietary algorithms, product designs, secret formulas.
- Strategic Plans: Merger and acquisition documents, future product roadmaps.
By tackling these high-risk assets first, you get the biggest security wins right away. This builds momentum and shows the value of the program, which makes it much easier to get buy-in when you're ready to expand the framework. It's no surprise the data governance market is exploding, driven by these high-stakes regulatory demands. The market was valued at USD 4.51 billion in 2024 and is projected to reach USD 19.38 billion by 2033.
Create Practical, Enforceable Policies
Your access policies are the rules of the road for your data. They need to be crystal clear, practical to follow, and—most importantly—enforceable through technology. A good policy is more than a vague statement; it provides concrete guidance. A solid starter policy should define who can access what data, under what specific conditions, and for what legitimate purpose.
The infographic below shows how these core components fit together to create a solid data access governance program.
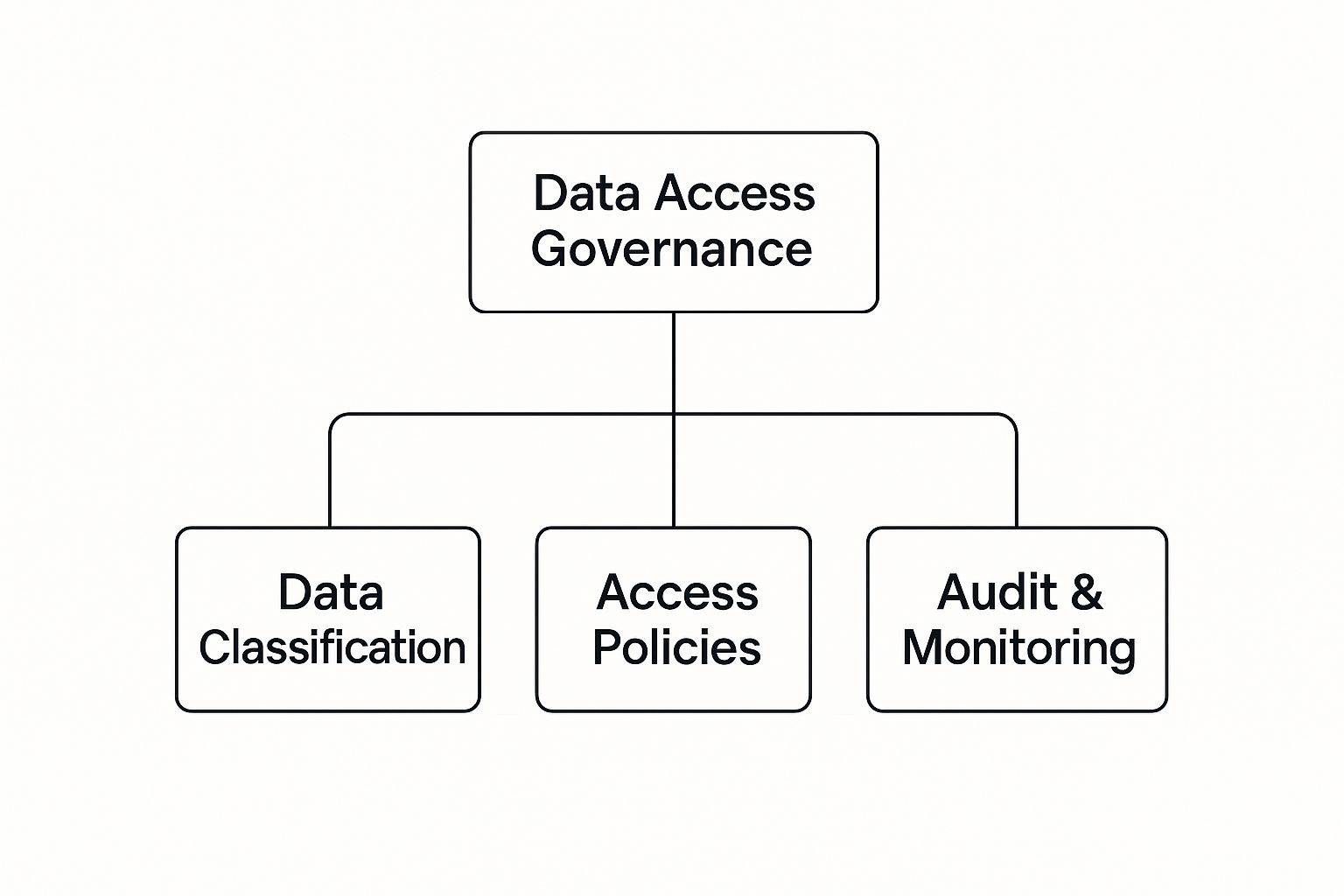
As the visual shows, it's the combination of data classification, clear access policies, and continuous monitoring that forms a complete governance structure. For example, creating targeted access policies for specific marketing campaigns can be a complex but vital task. To get a better sense of how data is used in that field, take a look at our guide on the role of machine learning in marketing. When you build your framework on these pillars, you create a system that is both secure and agile.
Meeting Compliance Demands with Smart Governance

For a lot of organizations, compliance isn't just another box to check—it’s the primary reason they invest in strong data access governance. Trying to navigate the maze of regulations like GDPR, CCPA, and HIPAA can feel like walking through a minefield. One wrong step can trigger massive fines and do lasting damage to your brand’s reputation.
This is where a smart governance framework stops being a cost center and becomes a critical investment in your legal and financial stability. These regulations aren't just about having policies written down somewhere; they demand that you can prove you have control over your sensitive data. You have to be ready to answer key questions on the spot: Who accessed customer data? When did they touch it? And why did they need it?
A solid data access governance program gives you the tools to answer these questions with total confidence. It creates a direct line between your internal controls and specific regulatory requirements, turning abstract legal jargon into concrete, everyday operational tasks.
Actionable Insight: Bridging Governance Actions to Compliance Requirements
It’s one thing to have governance policies, but it’s another to understand exactly how they satisfy legal mandates. This isn't about aimless box-ticking. It's about building a defensible posture that clearly demonstrates due diligence. A mature data access governance strategy provides a clean, clear audit trail that regulators can easily follow.
Here’s how core governance actions map directly to common compliance needs:
- Automated Access Logging: Regulations almost always demand a detailed history of who has touched sensitive data. Your governance tool should automatically create an immutable log showing precisely which users accessed which datasets and when—an absolute must for any forensic investigation.
- Periodic User Access Reviews: A key principle of data minimization is ensuring permissions don't stick around forever. Schedule quarterly or semi-annual reviews where data owners must re-certify access for their teams. This provides direct proof that you are actively managing and revoking outdated permissions.
- Role-Based Access Controls (RBAC): Implementing RBAC based on the Principle of Least Privilege shows regulators that access isn't handed out randomly. It proves you have a logical, structured system designed to limit data exposure to only what’s necessary for an employee's job.
Proactive governance is your best defense. Instead of scrambling to pull records during an audit, a well-implemented DAG framework means the evidence of your compliance is continuously generated and always ready.
A Practical Example in Healthcare
Think about a healthcare provider managing thousands of electronic patient records protected under HIPAA. The potential for a data breach is enormous, and the penalties for non-compliance are severe. In this world, a solid data access governance system isn't just a nice-to-have; it's completely non-negotiable.
In this scenario, a doctor needs to see a patient's medical history to provide treatment. The DAG system grants them "view-only" access to that specific patient's file and only for the duration of the treatment. It logs the exact time of access and the specific data viewed.
Meanwhile, a billing administrator needs to see the patient's insurance information but is blocked from seeing any clinical notes. Their access is restricted only to the financial data required for their role. If a security incident were to happen, the provider could instantly pull audit logs to show regulators exactly who accessed what, proving their controls were not only in place but also strictly enforced.
This is the kind of granular control that separates compliant organizations from those at risk. For anyone looking to build out their own internal rulebooks, our guide on creating a sample data governance policy offers a great starting point.
The market certainly reflects this urgent need for control. As global data volumes continue to explode, the data governance market is projected by some sources to expand from USD 5.38 billion in 2025 to USD 18.07 billion by 2032. This incredible growth, which you can read more about on Fortune Business Insights, is a direct response to organizations scrambling to manage and secure their data in the face of ever-increasing regulatory pressure.
Choosing the Right Governance Tools
A well-designed strategy is essential, but it’s the technology that brings it to life. Choosing the right tools for data access governance is what turns your carefully crafted policies into automated, enforceable actions. This isn’t just about buying software; it's about picking a technology partner that can grow with your business and adapt to your unique security needs.
The market for these tools is exploding for a simple reason: managing access manually just doesn't scale anymore. The global data access governance market was valued at around USD 8.7 billion in 2023 and is projected to hit USD 28.7 billion by 2033. This surge, noted in research from DataHorizzon, is a direct result of digital transformation pushing companies to find better ways to protect their most critical information.
Understanding the Main Tool Categories
When you start looking for solutions, you'll find the landscape can be a bit confusing. Many tools claim to handle access control, and while they often have overlapping features, they are each built with a different core purpose in mind. Getting a handle on these categories is the first step to making a smart decision.
Here are the main types of tools you’ll come across:
- Identity and Access Management (IAM): These are the foundational systems that answer two basic questions: who is a user (identity) and what are they allowed to touch (access). IAM handles things like user authentication, single sign-on (SSO), and broad, role-based permissions, mostly at the application or network level.
- Privileged Access Management (PAM): Think of these as the high-security vaults for your most powerful credentials. PAM tools are purpose-built to lock down "super user" or administrative accounts. They secure credentials, monitor what privileged users are doing, and control access for IT admins, developers, and anyone else with the keys to the kingdom.
- Specialized Data Access Governance (DAG) Platforms: This is a newer breed of tool designed to manage access right at the data layer itself. They plug directly into your databases, data warehouses, and cloud platforms to give you fine-grained visibility and control over who can query, view, or change specific data sets, tables, or even individual columns.
The right tool really depends on your biggest headache. If your main challenge is managing user logins for all your SaaS apps, an IAM tool is a great place to start. If your worst nightmare is a compromised admin account, then PAM should be your priority. But if you need to control who sees what inside your Snowflake or Databricks environment, a specialized DAG platform is exactly what you need.
How to Evaluate Your Options
A side-by-side comparison can help you map these tool categories to what your business actually needs. More often than not, the best setup involves a combination of these tools, as each one solves a different piece of the overall access puzzle.
To make things clearer, let's break down how these different technology solutions stack up. The following table highlights their primary use cases and key features.
Comparison of Data Access Governance Tool Categories
| Tool Category | Primary Focus | Best For | Example Capabilities |
|---|---|---|---|
| Identity & Access Management (IAM) | Authenticating users and managing broad application-level access. | Centralizing user logins, enforcing multi-factor authentication, and managing basic roles across multiple systems. | Single Sign-On (SSO), user provisioning/deprovisioning, password management. |
| Privileged Access Management (PAM) | Securing and monitoring high-privilege accounts (e.g., system administrators). | Preventing credential theft, monitoring sensitive IT operations, and controlling access to critical infrastructure. | Credential vaulting, session recording, just-in-time privileged access. |
| Data Access Governance (DAG) Platforms | Providing granular visibility and control over access to data itself. | Implementing fine-grained policies within data warehouses, monitoring data usage for analytics, and automating access reviews. | Data discovery and classification, policy-as-code, dynamic data masking. |
When you're ready to choose, look beyond the feature checklist. Ask practical questions. How well does it integrate with your existing cloud stack? Can it scale to handle your data growth over the next five years? What do its reporting and auditing features actually look like in practice?
It's also crucial to think about the future. As AI systems become more autonomous, their own data access needs governance. Our guide on AI governance best practices digs into how these principles extend to machine learning models—a critical factor for future-proofing your toolkit. The key to long-term success is picking a solution that solves today's problems while aligning with where your technology is headed tomorrow.
How a Fictional Company Implemented DAG
Theory is one thing, but seeing how these concepts play out in the real world is another. Let’s walk through the journey of "UrbanBloom," a fictional e-commerce company that sells sustainable home goods.
UrbanBloom was hitting that tricky phase of rapid growth where their old, informal ways of doing things started to break down. Their approach to data access governance was a perfect example—it was reactive, messy, and frankly, an accident waiting to happen. The trigger finally came in the form of a minor, but deeply unsettling, data leak. A former employee’s account was still active, and that tiny oversight was all it took.
This incident wasn't just a fire to be put out; it was the alarm bell that exposed just how vulnerable they were. This became the catalyst for building a formal DAG program from the ground up. But the first hurdle wasn't technical—it was organizational. Leadership needed to be convinced to open the budget, and employees were skeptical, worried that new controls would just slow them down.
Actionable Insight: Getting Started with a Practical Plan
The company appointed a senior IT manager as its new Data Governance Lead. She knew right away that a "boil the ocean" strategy was doomed to fail. Her first move was to secure executive buy-in. She framed the recent leak not as a simple mistake, but as a symptom of a systemic risk that threatened customer trust and the company's hard-won brand reputation. It worked. With a modest budget approved, she focused on a phased, pragmatic rollout.
The first step was to protect their crown jewels: customer data.
- Appoint a Data Owner: The VP of Marketing was formally named the Data Owner for all customer information. This was a crucial move. It placed accountability squarely on a business leader, not just on the IT department.
- Classify the Data: Working directly with the marketing team, they sorted customer data into tiers. Sensitive information like names and addresses—Personally Identifiable Information (PII)—was labeled "Confidential." In contrast, anonymized purchasing trends were classified as "Internal."
This simple classification exercise immediately brought clarity, showing everyone exactly where the tightest controls were needed most.
UrbanBloom’s key insight was that perfect governance was the enemy of good governance. By starting small with their most sensitive data domain, they could demonstrate value quickly and build momentum for the broader program.
Selecting Tools and Rolling Out Policies
With a clear scope defined, UrbanBloom started evaluating technology. They realized they didn't need a massive, all-in-one platform to get started. Instead, they chose a specialized DAG tool that plugged directly into their cloud data warehouse, giving them the fine-grained visibility they needed to see exactly who was querying customer tables and when.
The rollout was gradual and collaborative. They began with the marketing analytics team, working alongside them to define role-based access policies. For example, an analyst could access aggregated, anonymized sales data by default. But to see raw PII for a specific campaign analysis, they had to submit a request through the new system. The request was time-bound for one week and required electronic approval from the Data Owner (the VP of Marketing).
Instead of the pushback they had feared, the team actually appreciated the new clarity. No more guessing games about what data was appropriate to use. The results spoke for themselves: UrbanBloom successfully reduced its data exposure risk, automated its previously manual access review process, and created a scalable blueprint to extend data access governance across the entire organization. This real-world application of governance principles is also vital when considering future technology stacks, including how you manage access for automated systems. You can learn more by exploring some ideas on mastering AI model management.
Common Data Access Governance Questions
Once you move past the theory, data access governance gets real, fast. The day-to-day execution is where the rubber meets the road, and it’s where most teams run into practical hurdles. Let's tackle some of the most common questions that pop up when turning a governance plan into reality.
Who Should Ultimately Own Data Access?
This is the classic debate. While it’s tempting to hand this entire problem over to the IT department, that’s a mistake. Your IT team is absolutely essential for building and maintaining the technical guardrails, but ultimate ownership must sit with the business.
Think about it: who truly understands the data? The VP of Sales knows exactly what's in the CRM, how sensitive it is, and who on their team genuinely needs access to do their job. IT can't make that call.
In this model, the business leader is accountable for defining the rules, and IT acts as the custodian that enforces them. This setup ensures that access decisions are driven by real business needs, not just what's technically possible.
How Do We Handle Employee Pushback?
Nobody likes new rules, especially if they think it'll slow them down. Employees often hear "governance" and immediately picture bureaucratic red tape getting in the way of their work. The key to getting them on board is to be transparent and focus on what’s in it for them.
- Explain the "Why": Be upfront. The goal isn't to make their lives harder; it's to protect the company, its customers, and ultimately, their jobs from the fallout of a data breach.
- Highlight the Speed: Frame the new system as an upgrade. Instead of slow, manual email chains to get access, you're introducing automated, self-service workflows that grant the right access much faster.
- Start with a Pilot Group: Don’t try a "big bang" rollout. Pick a single, receptive team and get them up and running first. Their success will become your best internal case study.
When employees see governance as a system that provides clarity and secure self-service—rather than just a set of restrictions—they are far more likely to embrace it. For more ideas on how different data roles can collaborate, check out our previous articles on Datanizant.com which explore the dynamics of modern data teams.
Can We Afford to Implement This?
Sticker shock is real, and data access governance tools can look expensive at first glance. But you have to weigh that against the alternative. The cost of not having governance can be astronomical. A single data breach can lead to devastating fines, customer churn, and long-term brand damage.
The smart play is to start small. You don't need to boil the ocean and govern every piece of data on day one. Identify your most critical data assets—the crown jewels—and secure those first. A quick win there will prove the ROI and make it much easier to get the buy-in needed to expand the program over time.
At DATA-NIZANT, we provide the in-depth analysis you need to build robust, intelligent data strategies. Explore our expert insights on governance, AI, and cloud infrastructure to equip your organization for the future at https://www.datanizant.com.