Unlock business growth with cloud computing and data analytics. This guide explores the strategies, tools, and architectures top companies use to win.
-
-
🚨 16 Billion Credentials Exposed Don’t panic — but act fast. This massive exposure isn’t from a single hack, but years of infostealer malware silently collecting data from infected devices worldwide. 🧠 What Makes This Leak Different Unlike traditional data breaches, this represents a compilation of stolen credentials harvested over years by infostealer malware. These programs infected millions of devices, stealing passwords, tokens, and sensitive data from Google, Facebook, Apple, GitHub, Telegram, and banks. 🕵️♂️ How Infostealers Work Distributed through pirated software, malicious browser extensions, and fake updates. They silently harvest saved passwords, authentication cookies, crypto wallets, and session tokens.…
-
Discover effective strategies to tackle cloud migration challenges and ensure a smooth, successful transition for your business.
-
Transform your network security approach with proven strategies that actually protect. Learn from experts who've faced real threats head-on.
-
Discover effective endpoint management strategies to secure and optimize your devices. Learn how to turn device chaos into seamless control today!
-
The Real Cloud Cost Challenge Nobody Talks About Managing cloud costs is getting complicated. Migrating to the cloud doesn’t guarantee savings anymore. The growth of cloud services has created unpredictable billing, hidden resource sprawl, and budget overruns. These challenges aren’t just about saving money; they’re about controlling tech investments and making cloud spending a strategic advantage. The Complexity of Cloud Billing One of the biggest challenges is the complexity of cloud billing. Cloud providers offer many services, each with its own pricing and billing structure. This makes it hard to understand where your money is going and find areas to…
-
Last year around this time, over a warm cup of hot cocoa, I reflected on the NotPetya cyberattack, a global catastrophe that reshaped how we perceive cybersecurity threats. My detailed insights into the incident, shared in my post “NotPetya: Unmasking the World’s Most Devastating Cyberattack”, explored its massive economic, political, and technological impact. Fast forward a year, and here I am again, contemplating another major cyber incident—the Kaseya VSA ransomware attack. While the actors and the methods have evolved, the lessons remain eerily similar: we live in an increasingly connected world where vulnerabilities in software and systems can cascade into…
-
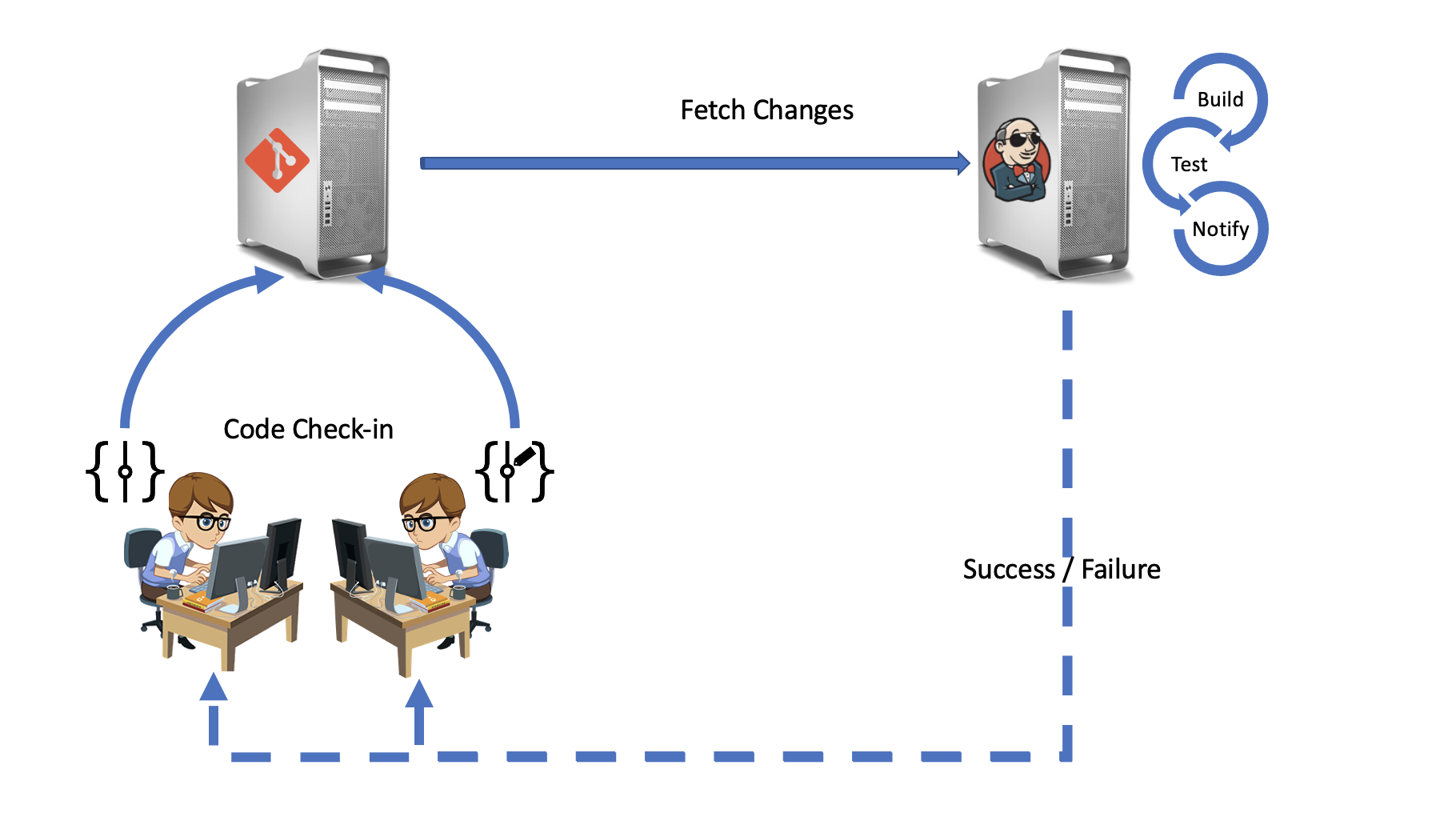
Introduction The aim of this blog is to provide a guideline for to build sophisticated continuous integration and continuous delivery pipelines. The Continuous Integration will be performed by JENKINS and many of its plugins. Especially the pipeline plugins. Jenkins is the open source platform agnostic tool written in Java for implementing DevOps pipeline. It is supported by a vast and generous open source community who helps in upgrading the product frequently. How does Jenkins Work? Jenkins work by using various plugins for different activities. The below image provides a visual representation of plugins per activity in Jenkins. Installation In order…
-
Why do we need CICD? Reduces code risk by integrating code from various sources at all phases of SDLC. Increases confidence among coders/developers Better quality of code Branching and shipping mechanism enables ready to ship code Code lineage and lifecycle management using systematic versioning Code quality and trend analysis Faster and consistent time to market Reduces cost CI: Continuous Integration The CI part of CICD can be summarized with: you want all parts of what goes into making your application go to the same place and run through the same processes with results published to an easy to access place.…
-
What Is DevOps? DevOps is a set of practices that combines software development (Dev) and IT operations (Ops). It aims to shorten the systems development life cycle and provide continuous delivery with high software quality. DevOps is complementary with Agile software development; several DevOps aspects came from Agile methodology. It involves communication and collaboration among all participants in the software development life cycle (SDLC). DevOps focuses on creating an ongoing feedback loop of analyzing, building, and testing while leveraging automation to speed the entire software delivery process. To achieve this kind of seamless and constant loop of software development and testing, you need to create cross-functional teams that can work together…